Hey! Listen! This post is part of a series on the Ubiquiti EdgeRouter Lite. Check them all out!
| Date | URL | Part |
|---|---|---|
| 2019-06-28 | Migrating away from the Ubiquiti EdgeRouter Lite | Migrated to a Netgate SG-1100 |
| 2019-02-03 | EdgeRouter CNAME records | Setup CNAME records |
| 2017-10-03 | Dyn DDNS on EdgeRouter | Setup DynDNS |
| 2017-04-25 | DuckDNS on EdgeRouter | Setup DuckDNS |
| 2017-01-08 | Ubiquiti EdgeRouter serial console settings | Serial console settings |
| 2016-11-29 | Ubiquiti UniFi controller setup on Raspberry Pi 3 | Install UniFi Controller |
| 2016-08-30 | EdgeRouter Lite Dnsmasq setup | Setup dnsmasq |
| 2016-06-13 | EdgeRouter Lite software upgrade | Firmware upgrade |
| 2016-05-12 | EdgeRouter Lite OpenVPN setup | OpenVPN server setup |
| 2016-04-29 | Ubiquiti EdgeRouter Lite setup | Initial setup |
Introduction
For years, I’ve been using and loving my Ubiquiti EdgeRouter Lite. For about $100, you’re not going to find a router with more features. In fact, most of Ubiquiti’s offerings are a very good value for the money. However, in the past year or so, Ubiquiti has seemed to have some issues with what direction they want to take as a company:
- A (seemingly pointless) re-brand from Ubiquiti/UBNT to UI.com (I wonder how much that domain name cost them)
- A (seemingly pointless) re-work of their forum software (it’s much more unorganized now)
- They (Ubiquiti) regularly ignored some of the most upvoted/requested ideas on their forums (which ironically, don’t exist on the new forum) to pursue new products
- They released the FrontRow wearable camera (not sure who asked for this product to exist)
- They released a series of network-connected LED lights and dimmer switches
- They released a series of VoIP phones
- They released the EdgeMax v2.0.0 firmware and almost immediately pulled it because of its beta-level quality. All releases since v2.0.0 seem to have had issues as well.
- They deprecated UniFi Video in favor of UniFi Protect (which only runs on Ubiquiti hardware)
- They put ads for UniFi Protect inside existing UniFi Video installations
- They removed SNMP from EdgeSwitch firmware
- They added phone-home telemetry to the UniFi Wireless firmware
It seems that Ubiquiti is throwing shit at a wall and seeing what sticks. Don’t get me wrong, I’d still recommend the EdgeRouter line to anyone who is currently using a router from BestBuy. However, I was growing tired and nervous of Ubiquiti’s decision making, so I resolved to replace my EdgeRouter with something slightly more stable and focused.
Requirements
Hardware
In terms of raw power, the EdgeRouter Lite is only a 500Mhz dual core MIPS CPU with 512MB of DDR2 RAM, so the bar was set pretty low. I knew I was going to be looking for a mini-PC form-factor, and only had a few requirements:
- Hardware that is small, low power, and fanless (this device is in my living room, not a server rack)
- Have Intel NICs (they generally have better compatibility with Linux/BSD than Realtek)
- Be around $250 or less, including RAM (but not storage)
With that said, below are the devices that I came up with in my search.
| Device | Link | Price | CPU | RAM | Storage | NICs | Price with 4GB RAM, no storage | BIOS updates | Comments |
|---|---|---|---|---|---|---|---|---|---|
| Jetway JBC313U591W-3160-B | Amazon | $249 | Quad Core Intel Celeron N3160 @ 1.60GHz | Up to 8GB DDR3 | mSATA | 2x Intel i211-AT | $273 | Infrequent | |
| APU2D4 | PC Engines | $134 | Quad Core AMD GX-412TC @ 1.00 GHz | 4GB DDR3 (included) | mSATA | 3x Intel i210-AT | $134 | Very frequent | Supports Coreboot |
| Fitlet 2 | Fitlet | $193 | Quad Core Intel Celeron J3455 @ 1.50GHz | Up to 16GB DDR3 | M.2 | 2x Intel i211-AT | $222 | Infrequent | |
| Protectli FW2B | Protectli | $179 | Dual Core Intel Celeron J3060 @ 1.60 GHz | Up to 8GB DDR3 | mSATA | 2x Intel i211-AT | $206 | Infrequent | Supports Coreboot |
| Shuttle DS77U | Amazon | $262 | Dual Core Intel Celeron 3865U @ 1.80 GHz | Up to 32GB DDR4 | 2.5" SATA and M.2 | 1x Intel i211 and 1x Intel i219-LM | $281 | Frequent | |
| Netgate SG-1100 | Netgate | $159 | Dual Core ARM Cortex A53 @ 1.20 GHz | 1GB DDR4 (included) | 8GB eMMC | 3x NICs (assuming Intel?) | $159 | Unknown | A customized ESPRESSObin |
Software
I have a relatively simple setup at home, so my requirements for a router OS were simple:
- DHCP
- leases and static mapping
- DNS
- Set internal domain name
- DNS forwarder
- Register DHCP leases and static mappings in DNS resolver
- Host overrides (e.g., CNAME records)
- Dynamic DNS updater
- Firewall
- 802.1Q VLANs
- Remote logging (to a remote server)
I considered Untangle NG Firewall, Sophos UTM Home Edition, Sophos XG Firewall Home Edition, ZeroShell, IPFire, ClearOS Community Edition, Smoothwall Express, and Endian, but chose not to pursue them because they were either proprietary, had limited functionality, or were abandoned completely. In the end, I narrowed my search down to pfSense, OPNsense, and VyOS.
| Software | Advantage | Disadvantage | Based on | Comments |
|---|---|---|---|---|
| pfSense |
|
|
|
|
| OPNsense |
|
|
|
|
| VyOS |
|
|
|
|
pfSense on the Netgate SG-1100
At first, I considered using the Shuttle DS77U with VyOS. However, VyOS is really made for advanced routing, which is not what I needed. Then, I thought about still using the DS77U, but with pfSense. However, I really wanted to support the pfSense project by purchasing from Netgate, and in my price range, my only option was the SG-1100. Even though x86 hardware arguably has more raw power than ARM hardware, the SG-1100 is no slouch. The ARM hardware is very specialized and can route at full gigabit (as seen by Lawrence Systems) and it has received some really great Reddit reviews.

The first ten minutes
Having never used pfSense before, I spent the first few minutes poking around in the web interface. The web GUI is snappy, and the device doesn’t seem to run too hot.
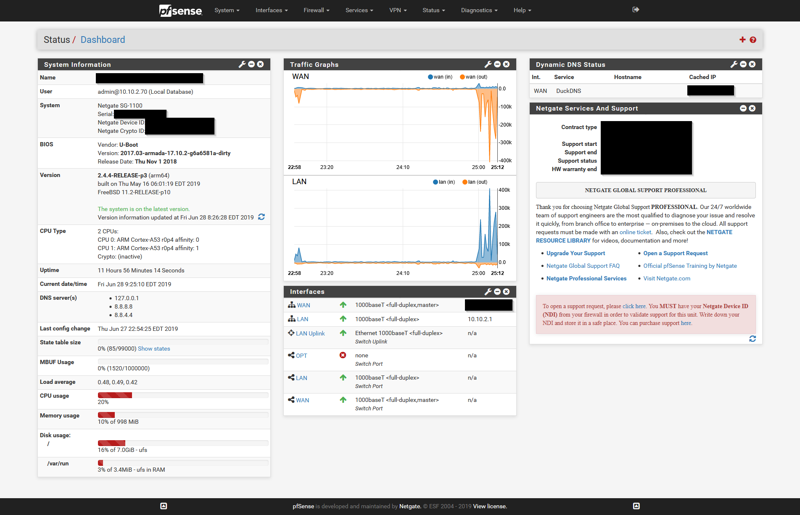
The first 24 hours
Before buying the SG-1100, I spent a good bit of time looking at my EdgeRouter configuration file and Googling how to duplicate it in pfSense. After going through the initial setup wizard, I went through the following tasks to port my EdgeRouter configuration over to pfSense.
- Setup new user accounts
- Setup my DHCP server
- Setup DHCP static mappings
- Setup CNAME records (which pfSense calls “host overrides”)
- Setup port forwarding rules
- Setup firewall rules
- Setup dynamic DNS
- Setup remote logging
- Setup configuration backup
I then shutdown all of my servers/devices, swapped out the routers, and powered up the SG-1100. To no one’s surprise, the SG-1100 booted up flawlessly and started handing out IP addresses.
pfSense vs EdgeOS
Obviously pfSense is going to be different than EdgeOS, but in the first day or two, a few things stuck out immediately.
- pfSense is based on FreeBSD, while EdgeOS is based on Debian Linux. I know nothing about how FreeBSD works under the hood, so my fear of the command-line is much greater on pfSense than on EdgeOS.
- That being said, pfSense has almost no command-line configuration. All of the configuration is done via the web interface, which has more options than I’ll ever use. Comparatively, EdgeOS had a relatively mediocre web interface, with all the advanced configuration being done via the command-line.
- The firewall setup on pfSense is very different from EdgeOS. I was used to a zone-based firewall with EdgeOS, but pfSense uses a more traditional interface-based firewall.
- pfSense has an implicit deny on the WAN inbound interface, and an implicit allow on the LAN outbound interface. EdgeOS only has this if you follow the setup wizard, whereas if you setup EdgeOS by hand, those rules are not there by default.
Both pfSense and EdgeOS can route gigabit, and both are able to utilize my 400/400Mbps FiOS internet connection. Running the command below to download 500Mb test file, I’m able to max out my connection with both routers, so I have no complaints there.
wget --report-speed=bits --output-document=/dev/null http://speedtest.wdc01.softlayer.com/downloads/test500.zip
I’ll spend the next few days tweaking all my pfSense settings, and then working on getting logging setup to push pfSense firewall logs to Graylog. Until then, I’m a happy SG-1100 and pfSense user!
-Logan